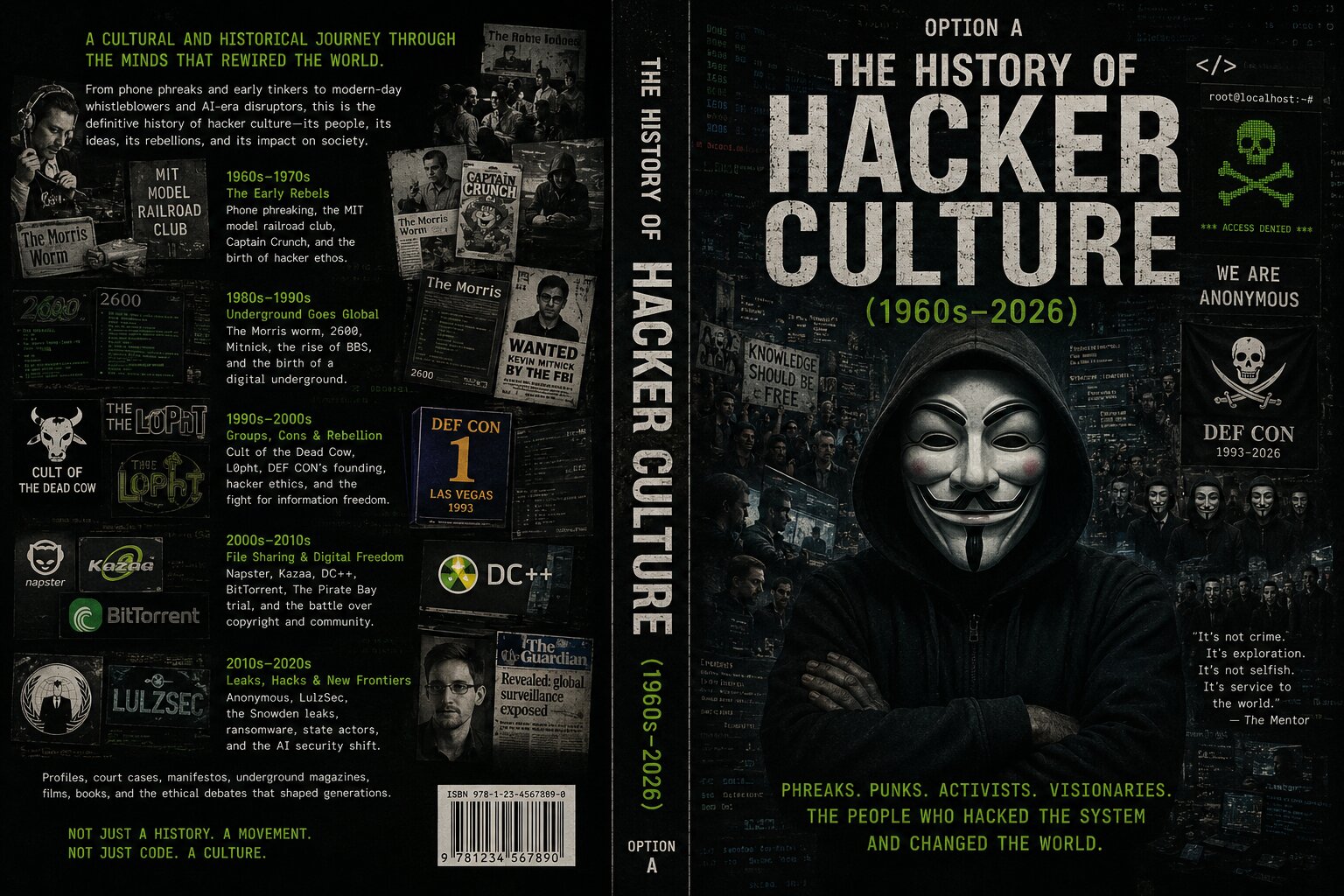
The history of hacker culture.1960s–2026 · Phreaks. Punks. Activists. Visionaries.
From a 2,600-hertz tone whistled by a blind boy in 1960 to the AI-augmented threat landscape of 2026: the definitive history of the people who hacked the system and changed the world. Plus the complete defense guide nobody else wrote.
We're the people who lived it.
Built by a team of researchers, security engineers, and journalists who grew up on BBS hubs, traded on DC++, watched Anonymous' rise from /b/, broke their teeth at DEF CON, and now ship code that defends global networks. Some of us were on the IRC channels when LulzSec was active. Some of us pulled malware apart for a living. Some of us wrote the patches you ran last Tuesday.
Around us grew a wider circle of more than ten contributors: security veterans who ran SOCs through the ransomware pandemic, ex-government threat hunters, defensive consultants, and academic historians who actually source-checked the legends.
Everyone chipped in. Some wrote chapters. Some argued with the chapters until they got better. Some pulled court documents to verify dates. Some walked the streets of memory: the BBS scene, Operation Sundevil, the Pirate Bay raid. The result is this book: a decade and a half of living inside the field, written by the people who did the work, and honest enough to be worth your time.
What you'll actually get.
Twelve parts, sixty-five chapters, fifteen appendices, three hundred glossary terms, two hundred answered questions. Written like a senior practitioner sitting next to you. Not a textbook. An education.
Origins
1960–1985
Phone phreaking, Joybubbles, Captain Crunch, the MIT Tech Model Railroad Club, the Homebrew Computer Club, and the underground press: TAP, 2600, Phrack.
The BBS
Golden Age
The Legion of Doom vs Masters of Deception. The Hacker Manifesto. Operation Sundevil. Kevin Mitnick on the run. Cult of the Dead Cow. L0pht testifies.
The
Internet Era
The Morris Worm. The script-kiddie wave. Napster, Kazaa, DC++. BitTorrent. The Pirate Bay. DEF CON, Black Hat, the conference circuit takes shape.
The
Dark Era
Anonymous. LulzSec. WikiLeaks. Stuxnet, the first cyber weapon. Snowden. Silk Road. Tor. The ransomware pandemic begins.
State-Actor
Age
The APTs. Equifax. SolarWinds. Colonial Pipeline. The cryptocurrency heists. Pegasus and the commercial spyware industry.
The
AI Era
ChatGPT changes the landscape. Deepfakes. AI-powered phishing at scale. Prompt injection. AI on the defense side. Where it all goes.
Defensive
Foundations
Threat models. Authentication, passkeys, encryption without mystery. Network security. The OS wars: Windows, macOS, Linux.
Linux &
The Tools
The history of free software. Kali, Parrot, Tails, Qubes. Command-line survival. 100+ defensive tools. OSINT and footprinting.
Personal
Security
Phone hardening. Home network. Browser. Email & phishing. Social media hygiene. Signal. The family security plan.
Professional
Defense
SOC, SIEM, EDR: the modern defense stack. Incident response. NIST, ISO 27001, MITRE ATT&CK, Zero Trust. Compliance. Cloud security.
Careers &
Education
Blue Team, Red Team, GRC, AppSec. The certifications that matter. Bug bounties: the legitimate hacker path. Books, channels, communities.
The
Future
Quantum computing & cryptographic apocalypse. The coming decade. Glossary of 300+ terms. 200+ questions answered.
From the blue box to the AI agent.
The Early Rebels
Underground Goes Global
Groups, Cons & Rebellion
File Sharing & Digital Freedom
Leaks, Hacks & New Frontiers
The AI-Era Frontier
It's not crime. It's exploration. It's not selfish. It's service to the world.
The Mentor · The Hacker Manifesto, 1986
One book. Two free bonuses.
Buy the Hacker Culture book and we'll add the Defender's Field Manual and the Privacy Toolkit, two complete companion volumes, at no additional cost.
HACKERCulture
The History of Hacker Culture
350+ pages, 12 parts, 65 chapters. The complete cultural and historical reference. Not just a history. A movement.
DEFENDField Manual
The Defender's Field Manual
Complete defense reference. SOC, SIEM, EDR. Incident response playbooks. NIST, MITRE ATT&CK, Zero Trust. Career roadmaps.
PRIVACYToolkit
The Privacy Toolkit
Phone hardening. Browser. Email. Signal. The family security plan. The privacy-first stack for ordinary humans in 2026.
- The History of Hacker Culture$39
- Bonus 1 · Defender's Field ManualFREE $19
- Bonus 2 · Privacy ToolkitFREE $19
- Lifetime updates & revisionsIncluded
Read it. Use it. Or it's free.
Take 14 days with the book. Walk through the history. Apply the defense playbooks. Set up the family security plan. If it doesn't feel like having a senior practitioner in the room with you, write to us and we'll refund every cent. Keep the bonuses. That's how confident we are in the work.
Noterad got the honour of launching this book.
This is the official collaboration between Noterad, the publisher of premium digital field guides, and a team of practitioners who have lived inside the cybersecurity field for fifteen years and inside hacker culture for far longer. We built this together, with the production polish of a publishing house and the honesty of people who actually do the work. You won't find this anywhere else.
Questions, answered.
Is this just a history, or is it an actual defense guide?
Both. Book One is the complete cultural and historical reference: sixty-six years of underground culture, the major figures, the landmark events. Book Two is the defensive mastery half: what every modern human, IT professional, executive, and journalist needs to know in 2026 to live and work safely on a network where every device is a target. You get both perspectives in one volume.
Will this teach me how to hack?
No. This book contains no exploit recipes, no darkweb operational guides, no offensive techniques as instructional content. It is a cultural history and a defensive reference. Readers interested in offensive security careers will find pointers to the legitimate paths: bug bounty programs, OSCP and similar certifications, authorized red-team work. Detailed offensive techniques themselves are taught through training programs and authorized engagements, not books available to the public.
Who is this book actually for?
People curious about hacker culture and how the modern internet got built. IT professionals, developers, and executives who need to understand the threat landscape they live in. Career changers wondering whether cybersecurity is for them. Parents who want to protect their families. Journalists, lawyers, and policymakers who work on these issues. Anyone who lived through some of this history and wants the receipts.
What format is the book in?
You get the main book and both bonuses as instantly downloadable Word .docx files (with PDF available on request). Read on phone, tablet, laptop, or print at home. Includes the full glossary and FAQ as searchable references.
Will I get future updates?
Yes. Every buyer is added to the lifetime update list. The cybersecurity field moves fast; when the book is revised (and it is, regularly), the new edition lands in your inbox at no additional cost. Major incidents get incorporated. New tools and techniques get added. The history doesn't change; the present-day chapters always reflect the latest landscape.
What if I read it and it's not for me?
Write to us within 14 days and we'll refund the full amount, no questions. The bonuses are yours to keep either way.
Who wrote and published this?
Written by a team of cybersecurity practitioners, researchers, and journalists with collective decades of experience in the field. Published in cooperation with Noterad, the field-guide imprint behind premium digital books on technology, privacy, and culture.
Do you write back if I have questions?
Yes. Every reader gets one direct reply per question. We read every email personally, usually within 48 hours. If you've started a security career path and have a question about which certification to take, where to apply, or how to set up a home lab, write to us. We're invested in seeing you succeed.
Come see the underground only practitioners know.
Three books. One price. Instant access. Sixty-six years of insider knowledge in your hands tonight. Read it. Use it. Defend something.
Get Instant Access · $77 $39